Long
before Air Force Maj. Kerry Baker stepped into the navigator seat of a
B-52 Stratofortress, he was a student tasked with drawing a portrait of
Abraham Lincoln for a school project. When his classmates saw his work,
they asked him to draw theirs too.
That childhood talent sparked a lifelong passion that he shares with aviation.
Over
the past two decades, Baker has become known as a premier artist for
the B-52 community, designing hundreds of unit patches, nose art pieces
and official heraldry that capture the heritage, morale and visual
identity of the 307th Bomb Wing mission and beyond.
"Proud is
not a word that I use in describing what I've done, but internally I am
proud of it," he said. "I'm very fortunate to have been given this
opportunity, or this canvas on which to work."
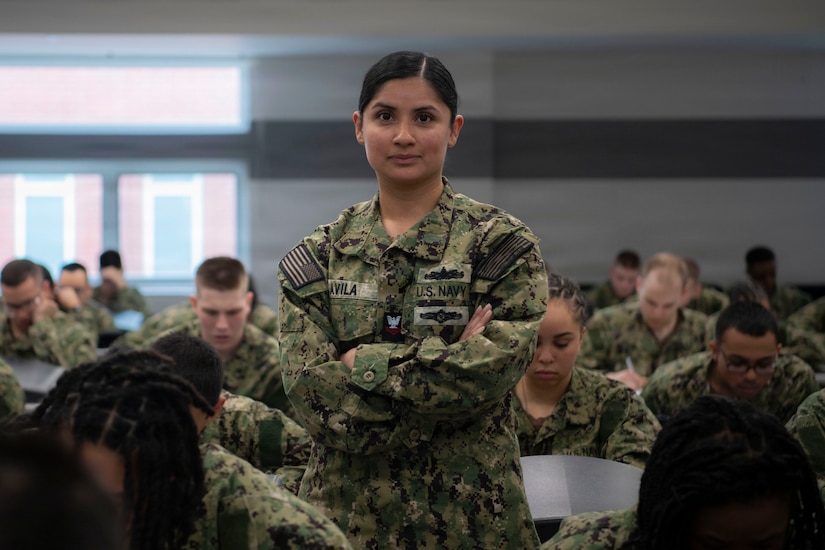
Now, the 307th Operations Support Squadron weapon systems officer is preparing to retire.
But
while Baker will soon leave the flight line behind, his legacy will
remain stitched into the very fabric of the 307th Bomb Wing and the
broader Air Force bomber community.
"I
had a top-down view of Kerry's artwork," said retired Air Force Lt.
Col. Joseph Jones, former vice commander of the 307th Bomb Wing. "He is
responsible for so much public relations and community engagement that
can never be replaced."
From the Canvas to the Cockpit
Baker's path to the Air Force was unconventional.
He
earned a degree in studio art painting from Truman State University in
Kirksville, Missouri, and was working for a civilian business until the
events of Sept. 11, 2001, changed the trajectory of his life.
Seeking to
serve his country, he initially visited a Marine Corps recruiter before
his life experience and college degree pointed him toward the Air
Force.
By
November 2002, he was
at officer training school and subsequently earned his wings. Driven by a
desire for a balanced family life and a love for the airframe, he
selected the B-52 Stratofortress.
Baker
served on active duty from 2003 to 2010 assigned to the 11th Bomb
Squadron and the 20th Bomb Squadron before transitioning to the Air
Force Reserve, joining the 93rd Bomb Squadron and later the
307th Operations Support Squadron. It didn't take long for his military
career and his artistic talent to collide.
"The
first patch I designed was for my navigator training class," Baker
said. "I knew nothing about the process, but I knew I didn't want to get
too crazy with the design because it had to be embroidered. That was my
first time designing something thoughtfully."
When
he arrived at the 11th Bomb Squadron, he drew an 8-foot-wide rendition
of a B-52 that remained hanging in the hallway for years. That
drawing established a reputation for him that quickly spread.
By
2006, he was designing deployment patches for the 20th Bomb Squadron,
tracking down vendors and ensuring his fellow airmen had their patches
before walking out the door.
Baker
continued accepting requests and creating artwork for missions,
often facilitating a platform to build relationships among the
307th Bomb Wing, other units, military branches and even countries.
"He
has been a vital part of our [War Department] and bomber community in
fortifying global strategy and reach," said retired Air
Force Brig. Gen. Robert Vanhoy II, former 307th Bomb Wing commander.
"His talent bonded units and created conversations across nations."
Art That Honors the Past
In his vast portfolio, Baker said a few pieces hold a deeply personal significance.
One
of those is the "100,000 Hours of Power" patch designed in 2014 to
commemorate a historic two-ship B-52 formation with more than 100,000
hours of collective flight time among the 20 aircrew members.
"A
patch is just a piece of cloth until you put it in someone's hand; then
it becomes a memory," Jones said. "Baker is responsible for that."
Baker also lent his talents to aircraft nose art.
In
2013, he designed "Red Gremlin II" for now retired Air Force Brig. Gen.
Paul Tibbets IV, adapting the original World War II B-17 Flying
Fortress nose art flown by Tibbets' grandfather.
The
artwork was applied to the B-52 in which Tibbets completed his
certification flight, and Baker later painted the design onto a leather
bomber jacket for him.
Another
memorable project was "My Baby II," a commemorative design honoring the
original 20th Bomb Squadron, which was shot down over Czechoslovakia in
August 1944.
Since
that project, Baker's artwork has become a staple of the unit's
participation in NATO Days, the largest European security show in
Ostrava, Czech Republic, that demonstrates the capabilities,
cooperation and interoperability of NATO allies and partners.
Leaving a Mark
As his retirement approaches, Baker reflected on his years of service and the unique mark he leaves behind.
"Flying
is great. I had a lot of fun flying ... but it's the people
that I've built lifelong friendships with," he said. "When I came to the
307th [Bomb Wing], for me it was a bunch of combat aviators that really
had an incredible sense of camaraderie. It felt like family right
away."
For the next generation of airmen harboring hidden creative talents, Baker offers a piece of parting advice.
"Absolutely
do not neglect it," he said. "Put it out there and let other people see
it, and you'll have opportunities to do special projects that people
enjoy and need."
Long
after Baker hangs up his flight suit, airmen walking the halls of
the bomb wing and flight lines across the globe will continue to wear
his artwork on their shoulders.
Through
his dedication to visual heritage, Baker ensured the pride, history and
morale of the bomber community will endure, one stitch at a time.